
Spear-phishing is on the increase, a survey of chief information security officers has found.
Spear-phishing is a type of phishing attack that targets specific individuals or organisations, typically through malicious emails.
Often, it is used to gain access to an individual’s account or impersonate a particular officer of someone involved in confidential operations.
The CISO view
Cyberark interviewed 12 leading security executives from Global 1000 organisations who have been steering their organisations towards a Zero Trust model an a range of questions including techniques that are being used to try to gain privileged access and the changing risk profile around remote working.
The adversary is looking at, ‘What access can I get?’ In a Zero Trust model, it is an identity and access management issue.
Mastercard SVP and Deputy Chief Security Officer Alissa (Dr Jay) Abdullah
A key finding from the report was that spear-phishing and impersonation attacks targeting high-level or high-value access is on the increase.
“Recently there has been a surge in spear-phishing campaigns targeting individuals who have direct access to a particular system the attacker is interested in,” the report found.
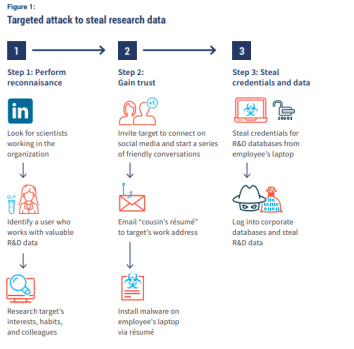
“First, the attacker determines who within the organisation – or at an associated third party – has access to a particular system.
“Then the attacker conducts a highly targeted social engineering campaign against this individual to steal their credentials.”
Targets may be IT administrators, and although as these are becoming harder to breach, more typically they tend to be an end user with high value access, the report found.
This cohort includes the likes of engineers with access to intellectual property; scientists with access to R&D data; claims managers with access to patient data; accountants with access to payment systems; or third-party analysts with access to customer records.
Another common tactic in recent attacks was impersonating a third party and asking an employee to transfer funds or provide data.
Methods used with this tactic include stealing credentials by creating a fake email; compromising a collaboration platform; or setting up a fake social media profile.
Trends
The report identifies a number of factors contributing to the rise in spear-phishing.
As more users are working remotely, and often doing so on insecure home Wi-Fi networks, they are offering attackers an easy entry access to their personal data via vulnerable social networks, especially as employees are also conducting more of their personal lives online through that same network.
Meanwhile, organisations are also embracing new collaboration tools and SaaS applications which generate new identities that can end up inadequately secured and monitored.
As end users have become a key target for attackers and the new working environment has become conducive to numerous identities being created, the report makes several recommendations to prevent your organisation from becoming a victim of spear-phishing:
- Identify “new” targets subject to increasing attacks
- Ensure MFA implementation is effective
- Protect higher- risk credentials in a PAM system
- Allow just enough access
- Drive awareness and cultural change
CyberArk is a global company providing identity security solutions. For more information on CyberArk, go to www.cyberark.com.
Comment below to have your say on this story.
If you have a news story or tip-off, get in touch at editorial@governmentnews.com.au.
Sign up to the Government News newsletter